A company can spend millions on cybersecurity tools and still lose sensitive data because nobody knows where that data actually lives, who can access it, or how exposed it has become over time. That is the problem driving the rapid adoption of data security posture management (DSPM).
Modern organizations store data across cloud platforms, SaaS apps, AI systems, employee devices, and third-party integrations. In many cases, security teams discover critical data risks only after an incident happens. An exposed storage bucket, excessive employee permissions, forgotten backups, or AI training datasets can quietly become major liabilities.
Data security posture management helps solve this visibility gap. Instead of focusing only on networks or endpoints, DSPM continuously monitors sensitive data itself — where it is stored, who can access it, how it moves, and whether it is properly protected.
This guide explains what data security posture management is, how it works, why it matters for AI environments, how DSPM tools compare, and what businesses should look for when choosing vendors. You will also learn practical lessons many organizations discover too late after deploying cloud and AI systems at scale.
What Is Data Security Posture Management?
Data security posture management is a cybersecurity approach focused on discovering, classifying, monitoring, and protecting sensitive data across cloud, SaaS, hybrid, and AI environments.
At its core, DSPM answers four critical questions:
- Where is sensitive data stored?
- Who has access to it?
- Is it properly secured?
- What risks exist right now?
Unlike traditional security tools that focus mainly on infrastructure, DSPM focuses directly on the data layer.
Simple Example
Imagine a healthcare company storing patient records across:
- AWS databases
- Google Drive files
- Slack conversations
- AI analytics systems
- Backup storage
A DSPM platform can identify:
- Which files contain protected health information
- Which employees or vendors can access them
- Whether encryption is enabled
- Whether unused datasets remain publicly exposed
- Whether AI systems are ingesting sensitive data improperly
This continuous visibility is what makes DSPM valuable.
Why Traditional Security Tools Are No Longer Enough
Many organizations already use:
- Firewalls
- SIEM platforms
- Endpoint protection
- Identity management systems
- Cloud security posture management tools
Yet data breaches continue increasing.
The reason is simple: companies often protect systems without understanding the actual data risk inside those systems.
A cloud server may appear secure while still containing:
- Misclassified sensitive data
- Over-permissioned accounts
- Old customer records
- Shadow AI datasets
- Forgotten backups
One of the biggest hidden problems is “data sprawl.” As companies adopt cloud apps and AI tools, sensitive information spreads faster than security teams can track manually.
DSPM was created specifically to address this challenge.
How Data Security Posture Management Works
Most DSPM platforms follow a similar process.
1. Data Discovery
The system scans environments to locate sensitive data across:
- Cloud storage
- Databases
- SaaS platforms
- Data lakes
- AI pipelines
- Development environments
It identifies information such as:
- Customer records
- Financial data
- Intellectual property
- Personal information
- Medical records
- API secrets
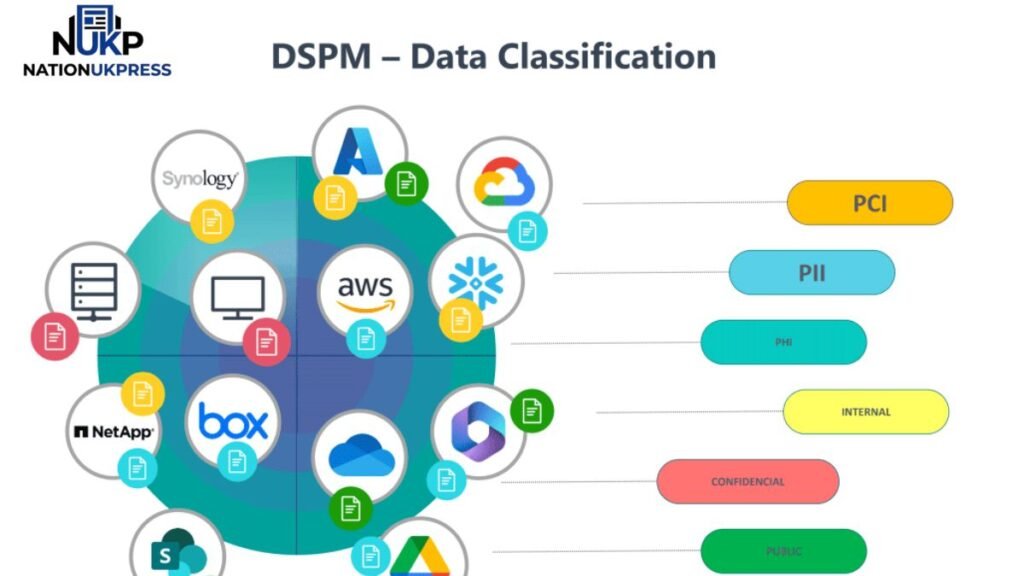
2. Data Classification
After discovery, DSPM tools classify data based on sensitivity.
For example:
| Data Type | Risk Level |
|---|---|
| Public marketing content | Low |
| Employee HR records | Medium |
| Payment card data | High |
| Healthcare records | Critical |
Advanced DSPM tools use machine learning to improve classification accuracy.
3. Access Analysis
The platform checks:
- Who can access the data
- Whether permissions are excessive
- Which accounts are inactive
- Whether third-party vendors have unnecessary access
This is where many organizations discover serious hidden risks.
A common real-world issue is “permission creep,” where employees accumulate access rights over years without review.
4. Risk Prioritization
DSPM platforms prioritize the most dangerous exposures.
For example:
- Publicly exposed sensitive data
- Unencrypted AI training datasets
- Dormant accounts with privileged access
- Misconfigured cloud storage
Instead of overwhelming teams with thousands of alerts, good DSPM tools focus on risks that truly matter.
5. Continuous Monitoring
DSPM is not a one-time audit.
The system continuously tracks changes such as:
- New data creation
- Access changes
- AI pipeline updates
- Cloud configuration changes
- New compliance violations
This ongoing visibility is essential in modern cloud environments.
DSPM vs CSPM vs Traditional Data Security
Many people confuse DSPM with CSPM.
Here is the practical difference.
| Security Approach | Primary Focus |
|---|---|
| CSPM | Cloud infrastructure configurations |
| DSPM | Sensitive data exposure and access |
| DLP | Preventing data movement or leakage |
| SIEM | Security event monitoring |
| IAM | Identity and access management |
Important Insight
A company can have perfect cloud configurations and still expose sensitive data because DSPM addresses risks that infrastructure-focused tools cannot fully see.
That distinction becomes even more important with AI systems.
Data Security Posture Management for AI
AI adoption is creating entirely new security risks.
Organizations now feed large amounts of sensitive information into:
- AI copilots
- Large language models
- Internal chatbots
- Machine learning pipelines
- Data enrichment systems
Many companies underestimate how quickly AI systems duplicate and spread data internally.
A Unique DSPM Challenge in AI
One overlooked issue is “training data residue.”
Even after organizations delete source files, fragments of sensitive information may remain inside:
- Vector databases
- Embedding systems
- Model caches
- Fine-tuned AI models
Traditional security tools rarely monitor this effectively.
Modern DSPM platforms increasingly include AI-aware capabilities that help organizations:
- Track sensitive AI training data
- Monitor AI access patterns
- Detect prompt leakage risks
- Audit model data exposure
- Identify unauthorized AI integrations
This is becoming critical for regulated industries like finance, healthcare, and legal services.
Another Overlooked AI Risk
Many organizations secure production AI models but ignore development environments.
In practice, development datasets often contain more raw sensitive information than production systems. DSPM tools can help detect these hidden exposures before they become breaches.
Common Data Security Posture Management Use Cases
Cloud Migration Security
Organizations moving to cloud platforms often lose visibility into sensitive data locations.
DSPM helps identify:
- Unsecured storage
- Duplicate datasets
- Excessive permissions
- Compliance gaps
Compliance Readiness
DSPM simplifies compliance with regulations like:
- GDPR
- HIPAA
- PCI DSS
- CCPA
Instead of manually searching for sensitive data, teams gain automated visibility.
Insider Threat Reduction
Not all breaches come from external attackers.
DSPM helps identify:
- Excessive employee access
- Dormant accounts
- Suspicious internal data exposure
Mergers and Acquisitions
During acquisitions, companies inherit unknown data risks.
DSPM can quickly assess:
- Sensitive data exposure
- Shadow IT environments
- Legacy access risks
This use case is growing rapidly but is still rarely discussed in most DSPM articles.
What to Look for in Data Security Posture Management Vendors
Not all DSPM vendors are equal.
Some focus heavily on cloud environments, while others specialize in SaaS or AI ecosystems.
Key Features to Evaluate
Accurate Data Discovery
False positives create alert fatigue.
Look for vendors with strong classification accuracy.
Multi-Cloud Visibility
Many businesses use:
- AWS
- Azure
- Google Cloud
- SaaS applications
DSPM tools should work across all major environments.
AI-Aware Security Features
This is increasingly important.
The best vendors now include:
- AI dataset monitoring
- LLM risk analysis
- Prompt exposure tracking
Risk Prioritization
Some tools generate too many low-value alerts.
Effective DSPM platforms prioritize exploitable risks.
Compliance Reporting
Automated reporting saves significant time during audits.
Integration Capabilities
DSPM should integrate with:
- SIEM platforms
- IAM systems
- Cloud providers
- Security orchestration tools
Common Mistakes Organizations Make With DSPM
Treating DSPM as Only a Compliance Tool
Many companies deploy DSPM purely for audits.
That limits its value.
The real strength of DSPM is operational visibility into live data risk.
Ignoring Data Ownership
DSPM tools work best when organizations clearly define who owns each dataset.
Without ownership accountability, risks often remain unresolved.
Focusing Only on Structured Data
Sensitive information also exists in:
- PDFs
- Chat logs
- Slack messages
- AI prompts
- Spreadsheets
Organizations that ignore unstructured data create major blind spots.
Forgetting About Old Data
One surprising reality:
Older forgotten datasets often become the highest-risk assets because they are poorly monitored but still contain sensitive information.
How DSPM Is Changing Security Teams
DSPM is reshaping how security operations work.
Traditionally, security teams focused mainly on:
- Perimeter defense
- Endpoint protection
- Network monitoring
Now, security is becoming increasingly data-centric.
This shift matters because attackers today often target data directly rather than infrastructure itself.
One emerging trend is closer collaboration between:
- Security teams
- Data engineering teams
- AI governance teams
- Compliance departments
DSPM sits at the center of that collaboration.
The Future of Data Security Posture Management
The DSPM market is evolving quickly.
Several major trends are emerging:
AI Governance Integration
DSPM platforms are becoming part of broader AI governance programs.
Real-Time Risk Remediation
Instead of only identifying problems, newer tools automatically fix issues such as:
- Excessive permissions
- Public storage exposure
- Encryption gaps
Identity-Centric Data Security
Future DSPM systems will increasingly combine identity behavior with data exposure analysis.
This helps organizations detect risky behavior faster.
Context-Aware Security
Modern DSPM platforms are moving beyond static scanning toward understanding business context.
For example:
- Is the exposed data actually sensitive?
- Is the user behavior abnormal?
- Is the AI model accessing data unexpectedly?
This contextual intelligence reduces alert fatigue dramatically.
FAQ
What is data security posture management in simple terms?
Data security posture management is a cybersecurity approach that helps organizations discover sensitive data, understand who can access it, identify risks, and continuously monitor security exposures across cloud and AI environments. It focuses directly on protecting the data itself rather than only protecting infrastructure.
How is DSPM different from cloud security posture management?
Cloud security posture management mainly focuses on cloud infrastructure configurations, while DSPM focuses specifically on sensitive data exposure, permissions, and security risks. CSPM protects systems, whereas DSPM protects the actual information stored within those systems.
Why is data security posture management important for AI?
AI systems often process large volumes of sensitive information. DSPM helps organizations monitor AI training datasets, track data exposure, manage AI access permissions, and reduce risks like prompt leakage or unauthorized model access. This visibility is becoming essential as businesses deploy generative AI tools.
What industries benefit most from DSPM?
Industries handling sensitive information gain the most value from DSPM, including healthcare, finance, legal services, government, SaaS companies, and ecommerce businesses. Any organization using cloud storage or AI systems can benefit from stronger data visibility.
What should companies look for in DSPM tools?
Organizations should evaluate DSPM tools based on discovery accuracy, multi-cloud support, AI security capabilities, risk prioritization, compliance reporting, and integration options. Strong visibility and actionable insights are usually more important than having the largest number of features.
Can small businesses use data security posture management?
Yes. Smaller businesses increasingly face cloud and AI-related data risks. Many modern DSPM vendors now offer scalable solutions that work for smaller teams without requiring large enterprise security operations.
Conclusion
Data security posture management is becoming a critical part of modern cybersecurity because organizations can no longer protect what they cannot see. As cloud adoption, SaaS sprawl, and AI systems continue expanding, sensitive data moves faster than traditional security practices can track.
DSPM gives businesses continuous visibility into where sensitive data exists, who can access it, and which risks require immediate attention. More importantly, it shifts security from infrastructure-focused thinking to data-focused protection.
The companies that succeed with DSPM are usually the ones that treat it as an ongoing operational strategy rather than a simple compliance checkbox. In a world increasingly shaped by AI and distributed cloud environments, understanding your data posture is quickly becoming as important as securing your network itself.